LAB 2: AUTO SECURE
Bài viết này hướng dẫn cấu hình bảo mật cho các thiết bị Cisco dùng công cụ Auto Secure. Trong bài này, các bạn sẽ biết về các dịch vụ được bật lên trong router Cisco một cách mặc định, những dịch vụ được cho phép bởi hầu hết các người quản trị. Các dịch vụ này, phải được tắt hoặc được cấu hình lại để tăng tính bảo mật cho các thiết bị. Việc xem xét các dịch vụ này là quan trọng. Một số dịch vụ, vì lý do lịch sử, được bật một cách mặc định.
Trong một hệ thống mạng, router Cisco có thể được dùng ở các vị trí
- Thiết bị ngoài rìa của hệ thống edge devices
- Firewalls
- Internals Router.
Các dịch vụ sau đây mặc định trong Cisco router có thể là các lỗ hổng bảo mật: BootP, CDP, FTP, NTP, Finger, SNMP, TCP/UDP minor services, IP source routing và Proxy ARP. Tất cả các lỗ hổng trên đều có thể bị khai thác bất chấp vị trí đặt router trong hệ thống mạng.
Các khuyến cáo của Cisco về cách dịch vụ này là như sau:
- Tắt tất cả các dịch vụ và các cổng (interfaces) không cần thiết.
- Tắt những dịch vụ quản trị như SNMP, HTTP, DNS.
- Tắt các dịch vụ ICMP Redirect, IP source routing.
- Tắt dịch vụ IP directed broadcast.
- Tắt dịch vụ proxy ARP.
- Đảm bảo việc truy cập terminal thông qua các cơ chế ident, TCP keepalive.
Người quản trị mạng không nhất thíet phải biết khai thác các lỗ hổng bảo mật này. Tuy nhiên, họ cần phải biết cách tắt các dịch vụ này đi. Tuy nhiên, tắt các dịch vụ này một cách riêng lẽ thì rất nhàm chán. Cisco IOS có một công cụ giúp tự động hóa quá trình bảo mật cho các thiết bị, đó là Auto Secure.
AutoSecure có từ IOS 12.3 trở đi. Bạn hãy dùng lệnh show version để kiểm tra IOS hiện hành của bạn có hỗ trợ công cụ này hay không.
BB3#
BB3#show version
Cisco IOS Software, 2801 Software (C2801-ADVENTERPRISEK9-M), Version 12.3(14)T4, RELEASE SOFTWARE (fc2)
Technical Support: http://www.cisco.com/techsupport
Copyright (c) 1986-2005 by Cisco Systems, Inc.
Compiled Thu 08-Sep-05 17:00 by kehsiao
ROM: System Bootstrap, Version 12.3(8r)T9, RELEASE SOFTWARE (fc1)
BB3 uptime is 1 hour, 4 minutes
System returned to ROM by reload at 04:32:03 PST Fri Dec 1 2006
System image file is "flash:c2801-adventerprisek9-mz.123-14.T4.bin"
This product contains cryptographic features and is subject to United
States and local country laws governing import, export, transfer and
use. Delivery of Cisco cryptographic products does not imply
third-party authority to import, export, distribute or use encryption.
Importers, exporters, distributors and users are responsible for
compliance with U.S. and local country laws. By using this product you
agree to comply with applicable laws and regulations. If you are unable
to comply with U.S. and local laws, return this product immediately.
A summary of U.S. laws governing Cisco cryptographic products may be found at:
http://www.cisco.com/wwl/export/crypto/tool/stqrg.html
If you require further assistance please contact us by sending email to
export@cisco.com.
Cisco 2801 (revision 6.0) with 118784K/12288K bytes of memory.
Processor board ID FHK1020F1BJ
2 FastEthernet interfaces
1 Serial(sync/async) interface
1 Virtual Private Network (VPN) Module
DRAM configuration is 64 bits wide with parity disabled.
191K bytes of NVRAM.
62720K bytes of ATA CompactFlash (Read/Write)
Configuration register is 0x2102
Công cụ auto secure chạy ở chế độ enable mode, cho phép nhanh chóng loại bỏ các mối đe doạ tiềm tàng trong hệ thống mạng Cisco của bạn. Lệnh này có hai chế độ hoạt động, chế độ tương tác và chế độ dòng lệnh.
Đầu tiên ta thử nghiệm chế độ tương tác.
BB3#auto secure
--- AutoSecure Configuration ---
*** AutoSecure configuration enhances the security of
the router, but it will not make it absolutely resistant
to all security attacks ***
AutoSecure will modify the configuration of your device.
All configuration changes will be shown. For a detailed
explanation of how the configuration changes enhance security
and any possible side effects, please refer to Cisco.com for
Autosecure documentation.
At any prompt you may enter '?' for help.
Use ctrl-c to abort this session at any prompt.
Gathering information about the router for AutoSecure
Ở mức đơn giản, router sẽ hỏi bạn rằng router có kết nối ra Internet hay không. Nếu router của bạn là một router nằm bên trong, bạn chọn NO.
Is this router connected to internet? [no]:
Sau đó AutoSecure sẽ tự động tắt một số dịch vụ:
Securing Management plane services...
Disabling service finger
Disabling service pad
Disabling udp & tcp small servers
Enabling service password encryption
Enabling service tcp-keepalives-in
Enabling service tcp-keepalives-out
Disabling the cdp protocol
Disabling the bootp server
Disabling the http server
Disabling the finger service
Disabling source routing
Disabling gratuitous arp
Tiếp theo, router sẽ hướng dẫn bạn cấu hình các banner. Các banner này cần mang các thông tin mang tính cảnh báo cho các truy cập trái phép vào routers.
Here is a sample Security Banner to be shown at every access to device. Modify it to suit your enterprise requirements.
Authorized Access only
This system is the property of So-&-So-Enterprise. UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED. You must have explicit permission to access this
device. All activities performed on this device are logged. Any violations of access policy will result in disciplinary action.
Enter the security banner {Put the banner between
k and k, where k is any character}:
$This is a banner for demo to VnPro users$
Router có thể yêu cầu bạn khai báo các mật khẩu cần thiết cho router của bạn.
Enable secret is either not configured or
is the same as enable password
Enter the new enable secret:
% Password too short - must be at least 6 characters. Password configuration failed
Enter the new enable secret:
Confirm the enable secret :
Enter the new enable password:
% Password too short - must be at least 6 characters. Password configuration failed
Enter the new enable password:
Confirm the enable password:
Configuration of local user database
Enter the username: vnpro
Enter the password:
% Password too short - must be at least 6 characters. Password configuration failed
Enter the password:
Confirm the password:
Configuring AAA local authentication
Configuring Console, Aux and VTY lines for
local authentication, exec-timeout, and transport
Securing device against Login Attacks
Configure the following parameters
Blocking Period when Login Attack detected: 2
Maximum Login failures with the device: 3
Maximum time period for crossing the failed login attempts: 5
Router tự động cấu hình SSH trên router.
Configure SSH server? [yes]:
Enter the domain-name: vnpro
Configuring interface specific AutoSecure services
Disabling the following ip services on all interfaces:
no ip redirects
no ip proxy-arp
no ip unreachables
no ip directed-broadcast
no ip mask-reply
Disabling mop on Ethernet interfaces
Securing Forwarding plane services...
Enabling CEF (This might impact the memory requirements for your platform)
Configuring the named ACLs for Ingress Filtering
autosec_iana_reserved_block: This block is subjected to
change by IANA. For an updated list, visit
www.iana.org/assignments/ipv4-address-space.
1/8, 2/8, 5/8, 7/8, 23/8, 27/8, 31/8, 36/8, 37/8, 39/8,
41/8, 42/8, 49/8, 50/8, 58/8, 59/8, 60/8, 70/8, 71/8,
72/8, 73/8, 74/8, 75/8, 76/8, 77/8, 78/8, 79/8, 83/8,
84/8, 85/8, 86/8, 87/8, 88/8, 89/8, 90/8, 91/8, 92/8, 93/8,
94/8, 95/8, 96/8, 97/8, 98/8, 99/8, 100/8, 101/8, 102/8,
103/8, 104/8, 105/8, 106/8, 107/8, 108/8, 109/8, 110/8,
111/8, 112/8, 113/8, 114/8, 115/8, 116/8, 117/8, 118/8,
119/8, 120/8, 121/8, 122/8, 123/8, 124/8, 125/8, 126/8,
197/8, 201/8
autosec_private_block:
10/8, 172.16/12, 192.168/16
autosec_complete_block: This block is a combination of the
autosec_iana_reserved_block, autosec_private_block, and
any packet with a source address of multicast (224/4),
class E (240/4), 0/8, 169.254/16, 192.0.2/24, and 127/8.
Enabling unicast rpf on all interfaces connected
to internet
Auto Secure sẽ tiếp tục hỏi bạn có muốn cấu hình router hoạt động như một firewall hay không.
Configure CBAC Firewall feature? [yes/no]: y
This is the configuration generated:
no service finger
no service pad
no service udp-small-servers
no service tcp-small-servers
service password-encryption
service tcp-keepalives-in
service tcp-keepalives-out
no cdp run
no ip bootp server
no ip http server
no ip finger
no ip source-route
no ip gratuitous-arps
no ip identd
banner motd ^CThis is a banner for demo to VnPro users^C
security passwords min-length 6
security authentication failure rate 10 log
enable secret 5 $1$hhKG$BsTam.8KKr1wMkq0qBpbw.
enable password 7 110A1016141D5A5E57
username vnpro password 7 070C285F4D06485744
aaa new-model
aaa authentication login local_auth local
line con 0
login authentication local_auth
exec-timeout 5 0
transport output telnet
line aux 0
login authentication local_auth
exec-timeout 10 0
transport output telnet
line vty 0 4
login authentication local_auth
transport input telnet
line tty 1
login authentication local_auth
exec-timeout 15 0
login block-for 2 attempts 3 within 5
ip domain-name vnpro
crypto key generate rsa general-keys modulus 1024
ip ssh time-out 60
ip ssh authentication-retries 2
line vty 0 4
transport input ssh telnet
service timestamps debug datetime msec localtime show-timezone
service timestamps log datetime msec localtime show-timezone
logging facility local2
logging trap debugging
service sequence-numbers
logging console critical
logging buffered
interface FastEthernet0/0
no ip redirects
no ip proxy-arp
no ip unreachables
no ip directed-broadcast
no ip mask-reply
no mop enabled
interface FastEthernet0/1
no ip redirects
no ip proxy-arp
no ip unreachables
no ip directed-broadcast
no ip mask-reply
no mop enabled
interface Serial0/1/0
no ip redirects
no ip proxy-arp
no ip unreachables
no ip directed-broadcast
no ip mask-reply
ip cef
access-list compiled
ip access-list extended autosec_iana_reserved_block
deny ip 1.0.0.0 0.255.255.255 any
deny ip 2.0.0.0 0.255.255.255 any
deny ip 5.0.0.0 0.255.255.255 any
deny ip 7.0.0.0 0.255.255.255 any
deny ip 23.0.0.0 0.255.255.255 any
deny ip 27.0.0.0 0.255.255.255 any
deny ip 31.0.0.0 0.255.255.255 any
deny ip 36.0.0.0 0.255.255.255 any
deny ip 37.0.0.0 0.255.255.255 any
deny ip 39.0.0.0 0.255.255.255 any
deny ip 41.0.0.0 0.255.255.255 any
deny ip 42.0.0.0 0.255.255.255 any
deny ip 49.0.0.0 0.255.255.255 any
deny ip 50.0.0.0 0.255.255.255 any
deny ip 58.0.0.0 0.255.255.255 any
deny ip 59.0.0.0 0.255.255.255 any
deny ip 60.0.0.0 0.255.255.255 any
deny ip 70.0.0.0 0.255.255.255 any
deny ip 71.0.0.0 0.255.255.255 any
deny ip 72.0.0.0 0.255.255.255 any
deny ip 73.0.0.0 0.255.255.255 any
deny ip 74.0.0.0 0.255.255.255 any
deny ip 75.0.0.0 0.255.255.255 any
deny ip 76.0.0.0 0.255.255.255 any
deny ip 77.0.0.0 0.255.255.255 any
deny ip 78.0.0.0 0.255.255.255 any
deny ip 79.0.0.0 0.255.255.255 any
deny ip 83.0.0.0 0.255.255.255 any
deny ip 84.0.0.0 0.255.255.255 any
deny ip 85.0.0.0 0.255.255.255 any
deny ip 86.0.0.0 0.255.255.255 any
deny ip 87.0.0.0 0.255.255.255 any
deny ip 88.0.0.0 0.255.255.255 any
deny ip 89.0.0.0 0.255.255.255 any
deny ip 90.0.0.0 0.255.255.255 any
deny ip 91.0.0.0 0.255.255.255 any
deny ip 92.0.0.0 0.255.255.255 any
deny ip 93.0.0.0 0.255.255.255 any
deny ip 94.0.0.0 0.255.255.255 any
deny ip 95.0.0.0 0.255.255.255 any
deny ip 96.0.0.0 0.255.255.255 any
deny ip 97.0.0.0 0.255.255.255 any
deny ip 98.0.0.0 0.255.255.255 any
deny ip 99.0.0.0 0.255.255.255 any
deny ip 100.0.0.0 0.255.255.255 any
deny ip 101.0.0.0 0.255.255.255 any
deny ip 102.0.0.0 0.255.255.255 any
deny ip 103.0.0.0 0.255.255.255 any
deny ip 104.0.0.0 0.255.255.255 any
deny ip 105.0.0.0 0.255.255.255 any
deny ip 106.0.0.0 0.255.255.255 any
deny ip 107.0.0.0 0.255.255.255 any
deny ip 108.0.0.0 0.255.255.255 any
deny ip 109.0.0.0 0.255.255.255 any
deny ip 110.0.0.0 0.255.255.255 any
deny ip 111.0.0.0 0.255.255.255 any
deny ip 112.0.0.0 0.255.255.255 any
deny ip 113.0.0.0 0.255.255.255 any
deny ip 114.0.0.0 0.255.255.255 any
deny ip 115.0.0.0 0.255.255.255 any
deny ip 116.0.0.0 0.255.255.255 any
deny ip 117.0.0.0 0.255.255.255 any
deny ip 118.0.0.0 0.255.255.255 any
deny ip 119.0.0.0 0.255.255.255 any
deny ip 120.0.0.0 0.255.255.255 any
deny ip 121.0.0.0 0.255.255.255 any
deny ip 122.0.0.0 0.255.255.255 any
deny ip 123.0.0.0 0.255.255.255 any
deny ip 124.0.0.0 0.255.255.255 any
deny ip 125.0.0.0 0.255.255.255 any
deny ip 126.0.0.0 0.255.255.255 any
deny ip 197.0.0.0 0.255.255.255 any
deny ip 201.0.0.0 0.255.255.255 any
permit ip any any
remark This acl might not be up to date. Visit www.iana.org/assignments/ipv4-address-space for update list
exit
ip access-list extended autosec_private_block
deny ip 10.0.0.0 0.255.255.255 any
deny ip 172.16.0.0 0.15.255.255 any
deny ip 192.168.0.0 0.0.255.255 any
permit ip any any
exit
ip access-list extended autosec_complete_bogon
deny ip 1.0.0.0 0.255.255.255 any
deny ip 2.0.0.0 0.255.255.255 any
deny ip 5.0.0.0 0.255.255.255 any
deny ip 7.0.0.0 0.255.255.255 any
deny ip 23.0.0.0 0.255.255.255 any
deny ip 27.0.0.0 0.255.255.255 any
deny ip 31.0.0.0 0.255.255.255 any
deny ip 36.0.0.0 0.255.255.255 any
deny ip 37.0.0.0 0.255.255.255 any
deny ip 39.0.0.0 0.255.255.255 any
deny ip 41.0.0.0 0.255.255.255 any
deny ip 42.0.0.0 0.255.255.255 any
deny ip 49.0.0.0 0.255.255.255 any
deny ip 50.0.0.0 0.255.255.255 any
deny ip 58.0.0.0 0.255.255.255 any
deny ip 59.0.0.0 0.255.255.255 any
deny ip 60.0.0.0 0.255.255.255 any
deny ip 70.0.0.0 0.255.255.255 any
deny ip 71.0.0.0 0.255.255.255 any
deny ip 72.0.0.0 0.255.255.255 any
deny ip 73.0.0.0 0.255.255.255 any
deny ip 74.0.0.0 0.255.255.255 any
deny ip 75.0.0.0 0.255.255.255 any
deny ip 76.0.0.0 0.255.255.255 any
deny ip 77.0.0.0 0.255.255.255 any
deny ip 78.0.0.0 0.255.255.255 any
deny ip 79.0.0.0 0.255.255.255 any
deny ip 83.0.0.0 0.255.255.255 any
deny ip 84.0.0.0 0.255.255.255 any
deny ip 85.0.0.0 0.255.255.255 any
deny ip 86.0.0.0 0.255.255.255 any
deny ip 87.0.0.0 0.255.255.255 any
deny ip 88.0.0.0 0.255.255.255 any
deny ip 89.0.0.0 0.255.255.255 any
deny ip 90.0.0.0 0.255.255.255 any
deny ip 91.0.0.0 0.255.255.255 any
deny ip 92.0.0.0 0.255.255.255 any
deny ip 93.0.0.0 0.255.255.255 any
deny ip 94.0.0.0 0.255.255.255 any
deny ip 95.0.0.0 0.255.255.255 any
deny ip 96.0.0.0 0.255.255.255 any
deny ip 97.0.0.0 0.255.255.255 any
deny ip 98.0.0.0 0.255.255.255 any
deny ip 99.0.0.0 0.255.255.255 any
deny ip 100.0.0.0 0.255.255.255 any
deny ip 101.0.0.0 0.255.255.255 any
deny ip 102.0.0.0 0.255.255.255 any
deny ip 103.0.0.0 0.255.255.255 any
deny ip 104.0.0.0 0.255.255.255 any
deny ip 105.0.0.0 0.255.255.255 any
deny ip 106.0.0.0 0.255.255.255 any
deny ip 107.0.0.0 0.255.255.255 any
deny ip 108.0.0.0 0.255.255.255 any
deny ip 109.0.0.0 0.255.255.255 any
deny ip 110.0.0.0 0.255.255.255 any
deny ip 111.0.0.0 0.255.255.255 any
deny ip 112.0.0.0 0.255.255.255 any
deny ip 113.0.0.0 0.255.255.255 any
deny ip 114.0.0.0 0.255.255.255 any
deny ip 115.0.0.0 0.255.255.255 any
deny ip 116.0.0.0 0.255.255.255 any
deny ip 117.0.0.0 0.255.255.255 any
deny ip 118.0.0.0 0.255.255.255 any
deny ip 119.0.0.0 0.255.255.255 any
deny ip 120.0.0.0 0.255.255.255 any
deny ip 121.0.0.0 0.255.255.255 any
deny ip 122.0.0.0 0.255.255.255 any
deny ip 123.0.0.0 0.255.255.255 any
deny ip 124.0.0.0 0.255.255.255 any
deny ip 125.0.0.0 0.255.255.255 any
deny ip 126.0.0.0 0.255.255.255 any
deny ip 197.0.0.0 0.255.255.255 any
deny ip 201.0.0.0 0.255.255.255 any
deny ip 10.0.0.0 0.255.255.255 any
deny ip 172.16.0.0 0.15.255.255 any
deny ip 192.168.0.0 0.0.255.255 any
deny ip 224.0.0.0 15.255.255.255 any
deny ip 240.0.0.0 15.255.255.255 any
deny ip 0.0.0.0 0.255.255.255 any
deny ip 169.254.0.0 0.0.255.255 any
deny ip 192.0.2.0 0.0.0.255 any
deny ip 127.0.0.0 0.255.255.255 any
permit ip any any
remark This acl might not be up to date. Visit www.iana.org/assignments/ipv4-address-space for update list
exit
access-list 100 permit udp any any eq bootpc
ip inspect audit-trail
ip inspect dns-timeout 7
ip inspect tcp idle-time 14400
ip inspect udp idle-time 1800
ip inspect name autosec_inspect cuseeme timeout 3600
ip inspect name autosec_inspect ftp timeout 3600
ip inspect name autosec_inspect http timeout 3600
ip inspect name autosec_inspect rcmd timeout 3600
ip inspect name autosec_inspect realaudio timeout 3600
ip inspect name autosec_inspect smtp timeout 3600
ip inspect name autosec_inspect tftp timeout 30
ip inspect name autosec_inspect udp timeout 15
ip inspect name autosec_inspect tcp timeout 3600
ip access-list extended autosec_firewall_acl
permit udp any any eq bootpc
deny ip any any
!
end
Router sau đó sẽ hỏi bạn có thực sự muốn áp dụng cấu hình do Auto Secure tự động sinh ra bên trên hay không.
Apply this configuration to running-config? [yes]:
Applying the config generated to running-config
The name for the keys will be: BB3.vnpro
% The key modulus size is 1024 bits
% Generating 1024 bit RSA keys ...[OK]
BB3#
*Dec 1 13:42:58.979: %SSH-5-ENABLED: SSH 1.99 has been enabled
BB3#
001204: *Dec 1 13:43:03.375 UTC: %AUTOSEC-1-MODIFIED: AutoSecure configuration has been Modified on this device
BB3#
BB3#
BB3#
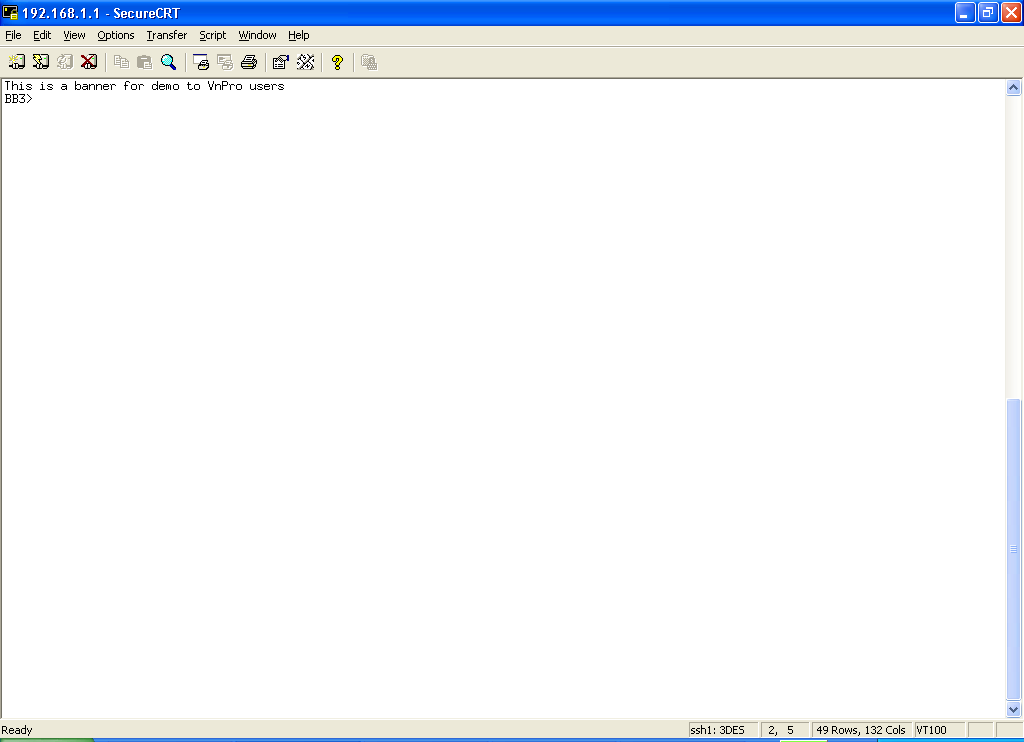
Khi bạn dùng Secure CRT truy cập vào router, bạn có thể thấy xuất hiện banner như trong hình dưới đây.
Thông tin khác
- » LAB 1: ISCW (PHẦN 2) (09.06.2023)
- » LAB 1: ISCW (08.06.2023)
- » IPSec GRE tunnel dự phòng cho leased-line (07.06.2023)
- » SỰ KIỆN HOT NHẤT TẠI VNPRO TỐI NAY: KHAI GIẢNG KHÓA HỌC CCIE (07.06.2023)
- » LAB PKI (PHẦN 2) (06.06.2023)
- » Lab PKI (Phần 1) (05.06.2023)
- » Configuring a Router-to-Router LAN-to-LAN Tunnel with a Router Initiating IKE Aggressive Mode (03.06.2023)
- » Quality of Service with Dynamic Multipoint VPN (02.06.2023)





